Brocade Crypto Key Generate Rsa Mod 1024
I have the n, d, e for RSA algorithm. However, I want to use privatekey to encrypt some string, generate USERCERTIFICATION, and use publickey for users to decrypt it and get the string.I know if I do so, the string can be easily decrypted by anyone, but security is not my concern at all, I just need that no one except me can generate the USERCERTIFICATION. Oct 02, 2015 SSH Config and crypto key generate RSA command. Use this command to generate RSA key pairs for your Cisco device (such as a router). Keys are generated in pairs–one public RSA key and one private RSA key. If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys. Jun 25, 2013 Cisco IOS CA server configuration. Mkdir flash:/CISCOCA conf terminal ip http server ip domain name networkology.net crypto key generate rsa modulus 1024 label CISCOCA crypto pki server CISCOCA issuer-name CISCOCA database archive pem password cisco123 grant auto lifetime certificate 365 lifetime ca-certificate 1095 database url pem disk0:/CISCOCA no shutdown exit. Table 1: Sample Times by Modulus Length to Generate RSA Keys Router 360 bits 512 bits 1024 bits 2048 bits (maximum) 4minutes,38 Morethan1hour. Crypto key generate rsa. Config t crypto key generate rsa exit Then ssh to the router and complete the config. Or just enable telnet if you can get away with it. Config t vty 0 4 transport input ssh telnet exit I have a perl script that does this to reset enable passwords.
Chilkat • HOME • Android™ • Classic ASP • C • C++ • C# • Mono C# • .NET Core C# • C# UWP/WinRT • DataFlex • Delphi ActiveX • Delphi DLL • Visual FoxPro • Java • Lianja • MFC • Objective-C • Perl • PHP ActiveX • PHP Extension • PowerBuilder • PowerShell • PureBasic • CkPython • Chilkat2-Python • Ruby • SQL Server • Swift 2 • Swift 3/4 • Tcl • Unicode C • Unicode C++ • Visual Basic 6.0 • VB.NET • VB.NET UWP/WinRT • VBScript • Xojo Plugin • Node.js • Excel • Go
| C++ example code showing how to generate an RSA public/private key.
| |||||
© 2000-2020 Chilkat Software, Inc. All Rights Reserved.
Telnet versus SSH
Many people continue to use Telnet for sensitive applications or access to critical systems. Telnet is CLEARTEXT, so all the data, including the login id is visible is someone intercepts that session
Here’s what this looks like using Wireshark an Open Source Protocol Analyzer when we use the Follow TCP Stream feature in Wireshark.
The next characters are red (the character I typed) and blue (the characters echoed back)
You clearly see the User Verification Prompt.Here's the telnet trace file.
Below you can see me typing in my username;
In this screenshot below you can see me entering the commandenable and the the enable password.
How to Enable SSH Version 1 on Cisco
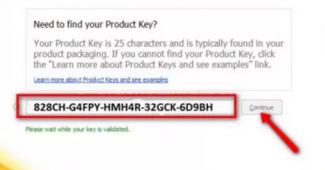
Before you can enable SSH you need to assign individual (or group) user IDs and passwords.
These are just login id's and are required regardless if you use Telnet or SSH.
To enable locally administered user IDs, use the following set of configuration commands. I would not suggest using the nopassword parameter.
Put your own data in the italized text.
Now when you telnet into the device you should see the Username prompt
| User Access Verification Username: fortunato Password: foghorn> |
Now that you have login id's created you can turn on SSH version 1.
To enable SSH, use the following set of configuration commands. I would not suggest using the nopassword parameter.
Put your own data in the italized text.
Watch dogs game key generator. foghorn#configure terminal Enter configuration commands, one per line. End with CNTL/Z. foghorn(config)#crypto key generate rsa % Please define a domain-name first.! common mistake when you do not the IP domain-name created foghorn(config)#ip domain-name thetechfirm.com foghorn(config)#crypto key generate rsa The name for the keys will be: foghorn.thetechfirm.com Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus [512]: 1024 % Generating 1024 bit RSA keys ..[OK] foghorn(config)#ip ssh time-out 120 foghorn(config)#ip ssh authentication-retries 5 foghorn(config)#end |
Now we'll try to capture the SSH login and as you can see the login data is no longer in clear text. Here's the SSH 1 trace file.
The moral of the story is not to use Cleartext logins if the device or application is sensitive.
To upgrade to even more secure SSH version 2, type in the following commands
| foghorn(config)#ip ssh version 2 foghorn(config)#no ip ssh version 1 foghorn(config)#end |
the SSH version 2 trace files are here
In this write up I used;
Brocade Crypto Key Generate Rsa Mod 1024 X
Wireshark Protocol Analyzer(free)
Putty Telnet/SSH Client(free)
Cisco Switch(not free)